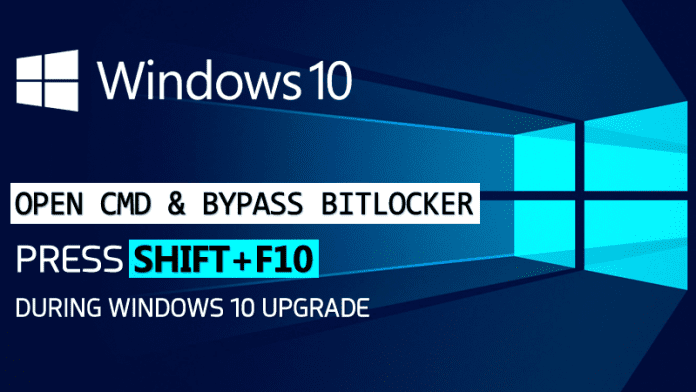
Security Researchers have found a Windows flaw that can bypass BitLocker Encryption and can have admin access during Windows 10 upgrade.
Hack Windows 10 PC By Holding “SHIFT+F10” During Upgrade
We all know about Bitlocker right? BitLocker is a full disk encryption feature included in Windows Operating system. However, Windows 10 systems have found a way to bypass BitLocker encryption.
Anyone with physical access to your Computer can access your files within few seconds. Attackers just need to hold down SHIFT+F10 during Windows 10 update procedure. The flaw is been discovered by security researcher Sami Laiho and this is the simple method of bypassing the Bitlocker.
Attackers who have physical access to your computer can open CLI (Command-line interface) with System privileges just by holding SHIFT+F10 while your Windows 10 computer is installing a new OS build.
Sami Laiho described that while our computer installs any new build (Windows 10 upgrade) the OS disables the BitLocker encryption while the Windows PE installs a new image of the main Windows 10 OS.
“The installation [Windows 10 upgrade] of a new build is done by reimaging the machine and the image installed by a small version of Windows called Windows PE (Preinstallation Environment),” Laiho says in his blog.”
“This has a feature for troubleshooting that allows you to press SHIFT+F10 to get a Command Prompt. This sadly allows for access to the hard disk as during the upgrade Microsoft disables BitLocker”
The SHIFT+F10 feature has existed with the earlier version of Windows like Windows 7 and Windows 8 as well. However, the flaw came into notice just after the arrival of Windows 10’s in-place upgrades. Attackers need to have physical access to the victim’s computer and can bypass BitLocker encryption to gain admin access to the system.
We all know that Windows updates take very long time to get installed and we have a bad habit of leaving our PC unattended during the Windows OS update procedure. So, the attacker can open the CLI debuggers and can perform malicious tasks with the user admin privileges without the need of any software.
Sami Laiho said, “The real issue here is the Elevation of Privilege that takes a non-admin to SYSTEM (the root of Windows) even on a BitLocker (Microsoft’s hard disk encryption) protected machine”. “And of course that this doesn’t require any external hardware or additional software.”
So, what to do now? Well, security researcher recommended users not to leave their PC during the update procedure and to block access to the CLI during windows updates by adding the file name “DisableCMDRequest.tag” to the “%windir%\Setup\Scripts\” folder.
You can watch the full video demonstration of the attack on Laiho’s blog.